ONSITE • REMOTE • CLOUD
Threat Detection
Threat Detection combines real-time monitoring (SIEM, EDR, XDR) with Threat Hunting, Cyber Threat Intelligence (CTI), and threat actor profiling to anticipate and mitigate risks proactively.
| Managed Threat Hunting | Compromise Assessment |
|---|---|
| Intelligence-driven, proactive threat detection using DFIR methodologies and tailored strategies. Our experts execute recurring hunts across networks, endpoints, and security platforms. | A one-time proactive security evaluation to detect hidden breaches that evade traditional detection methods. |
| Learn more | Learn more |
| SOC Less Service | Other Detection Improvement Services |
| Advanced detection and response capabilities without a traditional SOC, reducing operational costs while maintaining expert-driven security. | Encompassing Deception, Detection Assessment, SOC Empowerment and L3, these services enhance detection, optimize security operations, and bolster cyber resilience. |
| Learn more | Learn more |
What Is Threat Detection?
Threat Detection is the core discipline of identifying and responding to cyber threats before they can cause damage. It encompasses both reactive and proactive approaches, ensuring that organizations can swiftly detect, analyze, and mitigate potential security risks.
A Dual Approach: Reactive & Proactive Detection
-
Reactive Threat Detection focuses on identifying and responding to security incidents as they occur. This includes monitoring security logs, investigating alerts from SIEM, EDR, and XDR platforms, and deploying rapid Incident Response (IR) measures to contain threats.
-
Proactive Threat Detection shifts the focus from waiting for alerts to actively hunting for hidden threats within the infrastructure. This involves techniques like Threat Hunting, anomaly detection, and the deployment of advanced behavioral analytics to uncover potential cyber threats before they materialize.
However, effective Threat Detection requires more than just monitoring and hunting. To ensure optimal detection, two additional processes are essential:
-
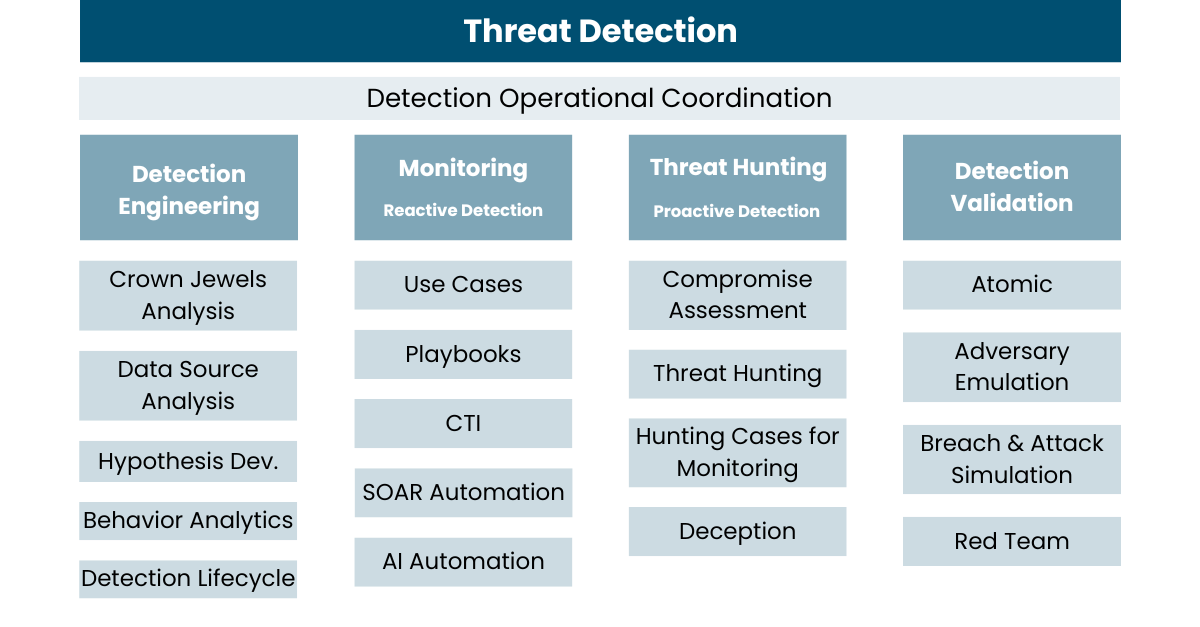
Detection Engineering: The foundation for successful reactive and proactive detection, focusing on data collection, rule & signature development, behavioral analytics, heuristics, and continuous improvement.
-
Detection Validation: Ensuring the effectiveness of detection mechanisms through Atomic Testing, Adversary Emulation, and Breach & Attack Simulation.
How do you know your systems are not compromised?
At One eSecurity, we offer a continuous, proactive threat-hunting framework that combines manual and automated analysis. Our methodology transforms threat management into a proactive operation, offering faster detection and response rates.
Our analyses are carried out through a comprehensive analysis of the environment, using both analytical and forensic techniques, targeting either global threats of specific profiled ones defined with the Client.

Why Threat Detection?
Prevention systems alone are insufficient to counter focused human adversaries who know how to get around most security and monitoring tools. - From SANS Institute.
Traditional prevention systems are not enough to stop determined adversaries who can bypass security controls and evade monitoring tools. Threat Detection provides a multi-layered approach, focusing on hidden, evolving, and sophisticated threats that conventional solutions often miss.
By leveraging intelligence-driven detection and minimizing reliance on specific technologies, Threat Detection reduces false positives and enhances visibility into unknown threats and advanced TTPs (Tactics, Techniques, and Procedures). It ensures organizations stay ahead of attackers by detecting what cannot be identified through automated systems alone.
Key benefits:
-
Wide variety of TTP and Threats continuously covered
-
Focus on what cannot be detected by other means
-
Intelligence-drive
-
Not high dependency on technology
-
Lower number of alerts and False Positive
-
Able to detect unknown threats

Much more than detecting Threat Actors
Threat Detection is not just about identifying malicious actors; it plays a crucial role across multiple areas of cybersecurity, enhancing Protection, Detection, and Response.
| PROTECTION | DETECTION | RESPONSE |
| - Detect weak configurations - Helps to evaluate tools such as EDR - May discover potential vulnerabilities - Support to improve configs and tools | - Use of Cyber Threat Intelligence - In-depth manual analysis of threats - Improve automated detections - Enhance teams: SOC, Purple/Red Team | - Reduce dwell time to zero in Response - Support other teams during EIR - Be a part of Incident Response - Enhance teams: SOC, Purple/Red Team |
How We Do It? - Advanced Threat Detection
A Traditional SOC is Not Good Enough
Effective Threat Detection requires a combination of reactive and proactive approaches to identify, analyze, and mitigate cyber threats before they cause significant damage. Also, our methodology ensures a continuous cycle of improvement and validation.
At One eSecurity, we enhance both reactive and proactive detection by leveraging our own detection platform – TRINITY. This platform integrates our Cyber Threat Intelligence (CTI), automates detection processes, and provides custom use cases to improve threat visibility and response capabilities.
Different approaches (initiatives) for advanced detection
| Detection Engineering |
|---|
| Detection Engineering is the process of creating and fine-tuning detection rules, use cases, and analytics to improve threat detection efficacy. See Detection Engineering |
| Reactive Services | |
|---|---|
| SOC-Less Service | A SOC-less service offers comprehensive cybersecurity monitoring and incident response without the need for an in-house Security Operations Center, managed externally by expert teams. See SOC-Less |
| Level 3 Analysis (Expert Escalations) | L3 Escalation provides advanced expertise for handling complex security incidents, escalated threat investigations, and deep forensic analysis beyond standard SOC capabilities. See L3 |
| SOC Empowerment | SOC Empowerment focuses on strengthening internal SOC teams by providing advanced training, expert guidance, and process optimization to maximize effectiveness. See SOC Empowerment |
| Detection Maturity Assessment | A structured assessment designed to evaluate an organization’s current detection capabilities and provide actionable recommendations for improvement. See Detection Maturity Assessment |
| Proactive Services | |
|---|---|
| Managed Threat Hunting | Managed Proactive Flexible Vendor agnostic Central service or complementary service See Managed Threat Hunting |
| Compromise Assessment | One-Shot Specific objective Incident Response-related, main Threat actors/TTPs, M&A, Bad practices identification, etc. See Compromise Assessment |
| Deception | Deception technology involves deploying decoys, traps, and lures to mislead attackers, detect malicious activities early, and gather valuable intelligence on threat actors. See Deception |
| Detection Validation |
|---|
| Once threats are detected, we validate the efficiency of detection mechanisms through: Atomic Testing: Evaluating individual detection rules against known threats. Adversary Emulation: Simulating real-world attacks to test SOC readiness. Breach & Attack Simulation: End-to-end validation of detection workflows and incident response. See Detection Validation |
What Advantages Do We Offer Compared To Our competitors?
Our Threat Hunting service formula is:
Threat Hunting = Response to Incident - Incident
At One eSecurity, our Threat Detection service goes beyond conventional approaches, providing unparalleled flexibility, expertise, and innovation. Here is what sets us apart:
Vendor Agnostic: Your Tools, Our Expertise
We seamlessly integrate with your existing cybersecurity infrastructure, eliminating the need for vendor lock-in. Our team of experts works with any SIEM, EDR, XDR, or security platform—all we need is access. Leveraging advanced queries, deep threat intelligence, and cutting-edge detection techniques, we immediately enhance your security posture. No need for costly migrations or unnecessary software purchases—we work with what you already have and make it better.
Tailored Solutions: Custom Detection for Your Unique Needs
Cyber threats vary, and so should your detection strategy. Our approach is fully customizable to match your infrastructure, integrating with:
-
Any security devices (e.g., routers, IDS/IPS, endpoint solutions)
-
Any cybersecurity tools (e.g., firewalls, threat intelligence feeds)
-
Other critical data sources (e.g., network traffic, log repositories, cloud telemetry)
-
Different types of Cybersecurity Architectures (on-prem, hybrid, multi-cloud environments)
Rather than one-size-fits-all solutions, we adapt to your specific threat landscape, ensuring enhanced detection and faster response times.
TRINITY: The Future of Threat Detection
Our proprietary TRINITY Threat Detection Platform is built by our R&D team to continuously automate, refine, and enhance proactive detection strategies. With TRINITY, we:
-
Identify emerging threats before they escalate
-
Automate complex detection workflows for increased efficiency
-
Leverage advanced analytics and AI to pinpoint anomalies and threats with precision
By combining human expertise with cutting-edge technology, TRINITY provides a powerful, proactive, and efficient approach to threat detection—giving you the edge over evolving cyber threats.
Related To Our Services
| Digital Forensics and IR | Emergency Incident Response | Cyber Threat Intelligence |
|---|---|---|
| One eSecurity Digital Forensics service is focused on system in-depth analysis, aiming at obtaining a traceable record of previous activity in order to answer any investigative questions. | One eSecurity Emergency Incident Response is aimed at clients who need agile response and support when a security incident happens. | The Cyber Threat Intelligence service by One eSecurity provides (both internally and for clients) knowledge and information on key threats for decision-making and forecasts of risk situations on IT systems and networks. |
| Learn more | Learn more | Learn more |